Introduction
Have you ever received the advice, “use a strong password.”? I’m sure most of you have. Maybe in your personal life by a family member whom you’ve looked to for advice on securing your bank or social media accounts. Or perhaps by an information security professional who just completed a security assessment for your firm. Then there are those penetration test reports where we commonly see “weak password policy” findings. Surely, somewhere, sometime, you’ve received this advice. But what exactly is a strong password? What does that mean? Continue down the page, and we will completely demystify strong passwords and dispel many common password-strength misconceptions.
The Password Problem
Let’s first set the stage and describe the problem. You have hundreds of online accounts. Passwords are the go-to authentication mechanism for just about everything, from online banking to social media to shopping.
When was the last time you were able to rattle off 100 random facts? Indeed, it’s not possible to remember the password for hundreds of online accounts.
Passwords are hard to remember. So, what do we do? Well, since passwords are hard to remember, we only have a few passwords we use for every account. You know what I mean. Maybe you use Yankees1964 for your bank account and Yankees1964! for your social media accounts. Then you think you’re super clever and use Y@nkees1964! for your Amazon account. While you’re at it, you use Y@ankees1964!! for your work password.😀
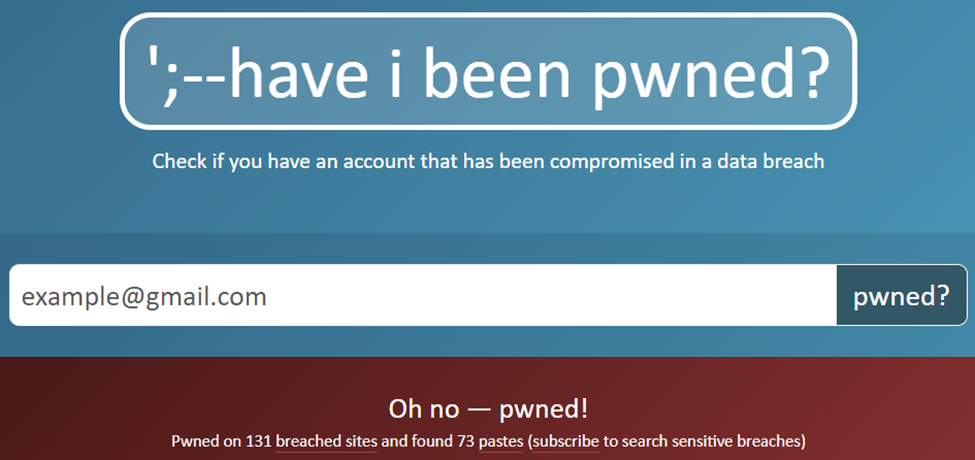
The hard truth is that once one service gets breached, it’s only a matter of time before attackers take those usernames and passwords and try them on other services. This is known as Credential Stuffing. That’s one of the biggest threats against passwords.
Password Strength Misconceptions
Misconception: Using special characters makes the password stronger. Not exactly. When I talk to people about passwords, they often ask if replacing letters with numbers or adding special characters helps make a password stronger. The truth is that it depends. Let’s use the example password above: Y@nkees1964!!. You may think that a 13-character password with symbols and numbers and a capital would be strong. A password like this would be trivial to crack, depending on the hashing algorithm used. So, complexity is excellent, but if you’re using dictionary words in a 13-character password, it really doesn’t make the password any stronger.

Using the same example, you may have been led to believe that adding an “!” at the end or another symbol increases strength. Unfortunately, that’s not the case. Because many password policies require special characters and because attackers know humans are creatures of habit, they know that a large number of passwords will begin with a Capitol letter and end with an “!”. This logic is even built into password-cracking systems, which is a whole other discussion in itself.
What is a STRONG Password?
Fact: The number one determining factor of a STRONG password is length. Longer is always stronger. That is fairly self-explanatory. Shorter passwords are easier to guess. Shorter passwords are also easier to brute force. Brute forcing is when you try every possible combination of a password until you get a match.
Another factor is something called entropy, which in this context means a lack of order or predictability. Unfortunately, it’s hard for us humans to remember intentionally random things. So, a password that has high entropy would be “randomly” generated. For example, take this randomly generated password: LTWCu5b11Qwp9$Hnnth%2Or%vqG. This password is LONG, and the characters are random, which increases the entropy. High-entropy passwords are much more difficult to guess than low-entropy passwords. The password I just showed is 27 characters and is a random set of characters. This is not getting cracked or guessed or brute-forced anytime soon.

Don’t Rely on Passwords Alone
Obviously, it’s an impossible task to remember one 27-character password, let alone hundreds. That’s the purpose of a Password Manager. With tools like 1Password, Bitwarden, etc., you can easily create and manage STRONG passwords for every account. The caveat here is that you MUST maintain and STRONG “master password” that you use to sign into the password manager. Then when you’re finished creating that strong master password, be sure to secure your password vault with mutlficator authentication. Mutlifactor authentication can be a saving grace should there be a compromise of master password. Now, the great thing is that now you only need to remember that one master password, and you’ve got access to all the rest.
But don’t trust passwords alone. My own personal recommendation is to “salt” your passwords with a secret that you do not store anywhere online. This salt can be a short pin code or a word. The idea is that you add this somewhere in your password but you don’t store it in your vault. This can add a little added protection for your most sensitive accounts, incase the password vault is compromised.
Password Dos & Don’ts
Let’s round this post out with some high level things to do and not to do.
- DO use a password manager, set a STRONG master password, and enable multifactor authentication.
- DO use STRONG, unique passwords for all accounts. Go back and change the accounts where you’re using the same password more than once.
- DO add spaces in your password. Think of it as a passphrase.
- DO “salt” your passwords if you so choose
- DON’T use easily guessable or publicly available information for your passwords, such as your birthday, address, or pet name.
- DON’T use the same password for multiple sites. You should aim to use a strong, unique password for every account.
- DON’T use dictionary words that are commonly found together.
Conclusion
I hope you found this information helpful, informative, educational, or slightly entertaining. If you have made it this far and are still unsure what a strong password is or what NOT to do when it comes to passwords, please feel free to reach out to me and I’d be happy to discuss this further.